Posts
1919Following
HiddenFollowers
HiddenAlpha Chen
alphahttps://tratt.net/laurie/blog/2022/how_might_generative_ai_change_programming.html
Is programming the best mechanism of turning specifications into software? There are certainly cases when the answer is “no”, whether that’s due to the use of domain specific languages, or glueing existing systems together in some way. That said, the history of software so far suggests that, to misquote Churchill, programming is the worst mechanism for turning specifications into software except for all those other forms that have been tried from time to time.
…
I find it easier to understand this by considering the problem in reverse. For example, imagine if you converted all the hashmaps in your favourite bit of software into arrays: you’d have exactly the same “functionality” but your software would probably become unpleasantly slow. In other words, the (correct) use of hashmaps is part of the specification — however, very few non-programmers would have thought to specify their use. As this suggests, user-level specifications are almost never complete — they leave out things that a good piece of software must address. Programming is the means by which we both understand what’s been left out and fill in the resulting blanks.
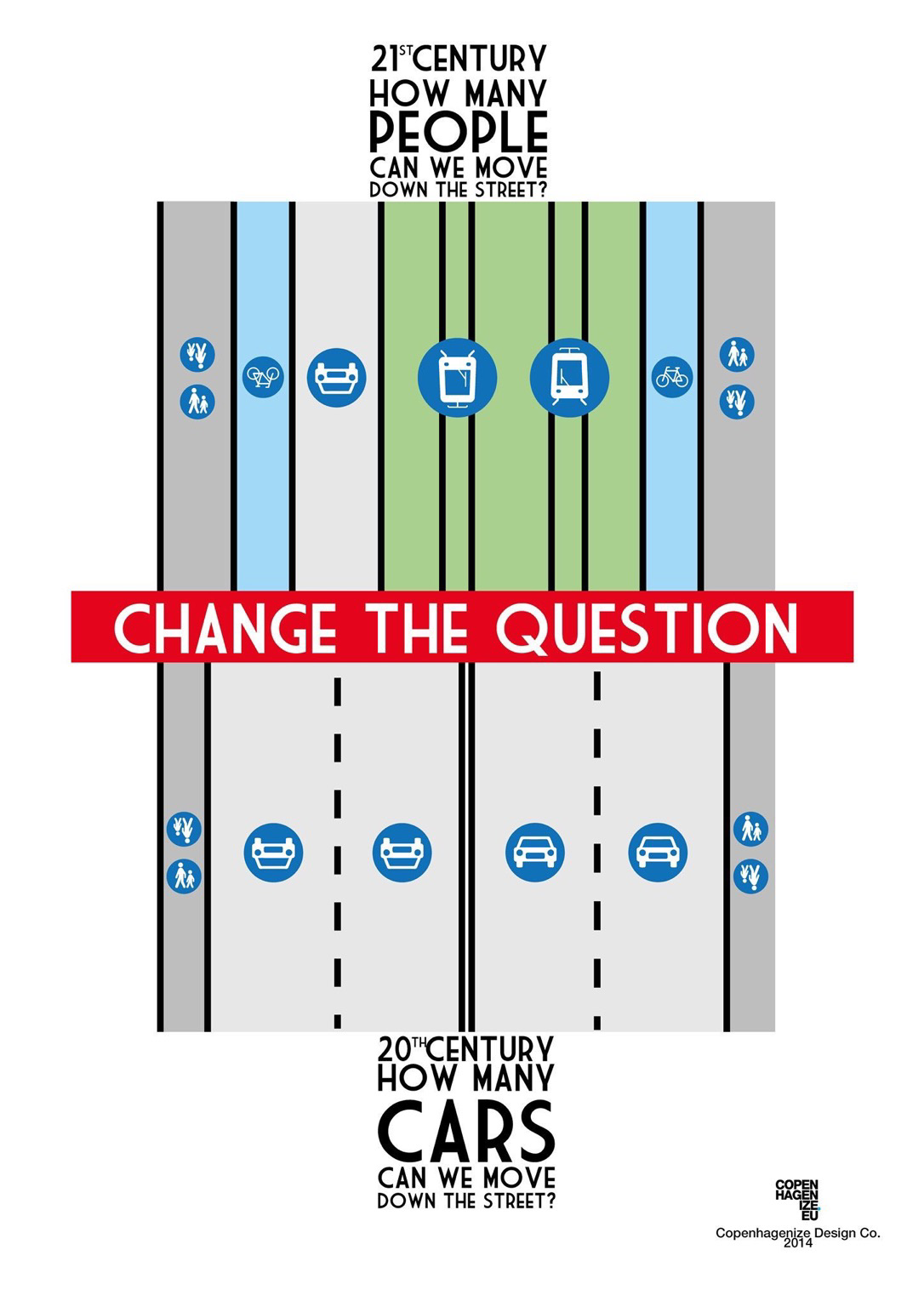
Brent Toderian
BrentToderian@mastodon.onlineLet’s talk honestly about your city.
If your city still thinks that the job of streets is to move cars, you have LOTS of work to do.
If your city thinks that the job of streets is to move people, that’s really important progress.
But never forget that streets are for a LOT more than just movement. Great streets are places for people to NOT WANT to move, or to want to move really slowly.
#cities #urbanism #transportation #cars #streets #people
Graphic via @Colvilleandersen
RT twitter.com/@vixenvalentino: @emmaogreen “The Case For Washing Hands Forever” by Emma Green
“Ignaz Semmelweis believes people should clean their hands before delivering babies, and that women shouldn’t die of preventable childbed fever.
What a fucking freak that guy was.” https://twitter.com/vixenvalentino/status/1608329856424591361
Alpha Chen
alphaAkkoma/Pleroma has the first feature, thankfully, but the second is so direly needed.
RE: https://lol.camp/objects/185529c7-04d3-4493-904e-365c5dbc81a1
Mindy Weisberger (she/her)
laminda@mastodon.socialTonight I decided to add candy eyes to our chocolate-dipped strawberries, only to learn that when it comes to desserts there is a very, very fine line between “whimsical” and “cursed”
Emily Aviva Kapor-Mater 🏳️⚧️
emilyaviva@tech.lgbtMy kids are watching this classic scene from Sesame Street and are just as confused as the Yip Yips. They have absolutely no conception of what this thing is. The humor of the scene has truly come full circle.
Alpha Chen
alphaThis is exactly why most technical conference talks fall flat for me.
RE: https://mastodon.social/users/wallingf/statuses/109593738651113883
Heather Buchel
hbuchel@hachyderm.ioI have this joke about one of the most coveted skills a software engineer can have is "looking at it" because early on in my career I worked with some developers that would tell me their work was done, because it compiled or whatever, but when actually used in context with the rest of the software (e.g. loaded into a UI or to the point a person had to interact with it) it was in fact broken still. So I would play the "did they look at it" game, because most often they had not.
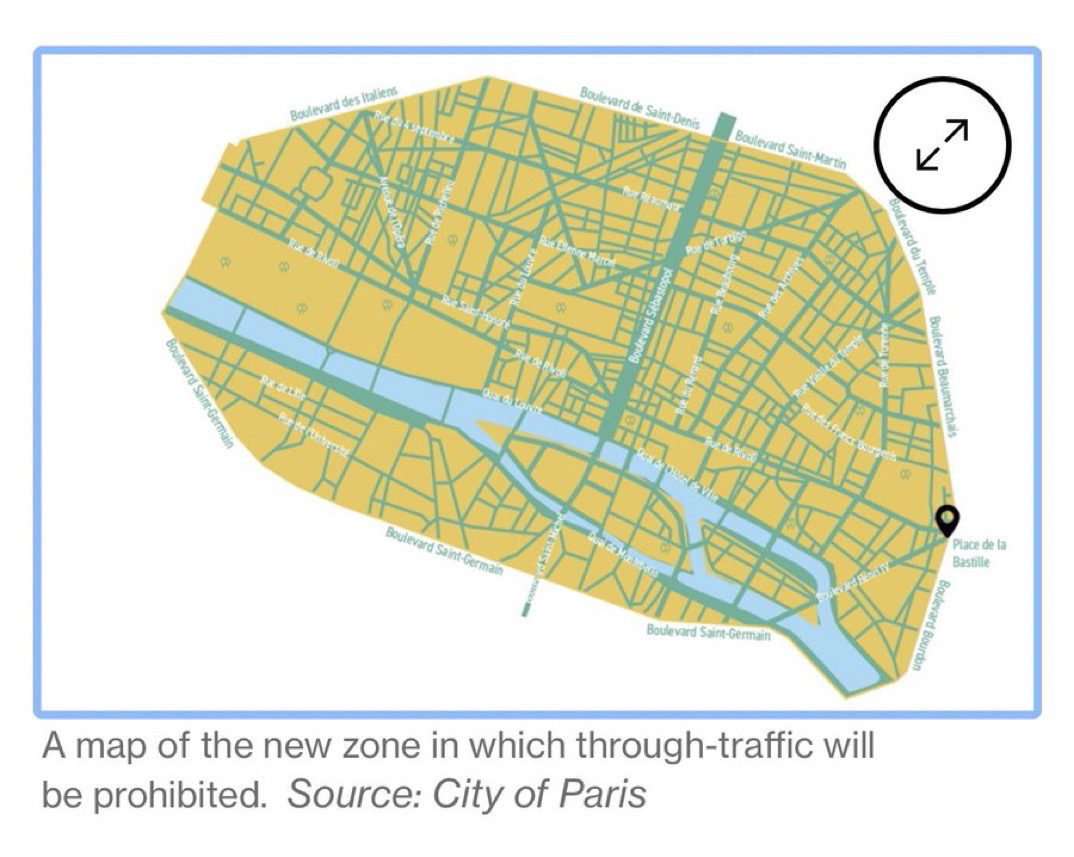
Brent Toderian
BrentToderian@mastodon.onlineIn 2024, Paris will ban non-essential vehicle thru-traffic from its city center. The plan is expected to cut around half of daily car journeys thru the core. Residents, public transit, emergency vehicles, & people with disabilities will find it EASIER to move. Via @citylab
https://www.bloomberg.com/news/articles/2022-02-18/paris-is-banning-traffic-crossing-the-city-center-from-2024
TProphet
tprophet@defcon.social1/ A lot of people have been asking for an explainer on what is going on with Southwest Airlines and the massive meltdown that occurred. Hi, I'm TProphet. I write the Seat 31B travel blog (https://www.seat31b.com) and closely follow the airline industry. More importantly, I have a friend whom Southwest abandoned in Las Vegas until New Year's (along with his cat), and there was literally nothing I could do for him. Ready? Let's dive in.
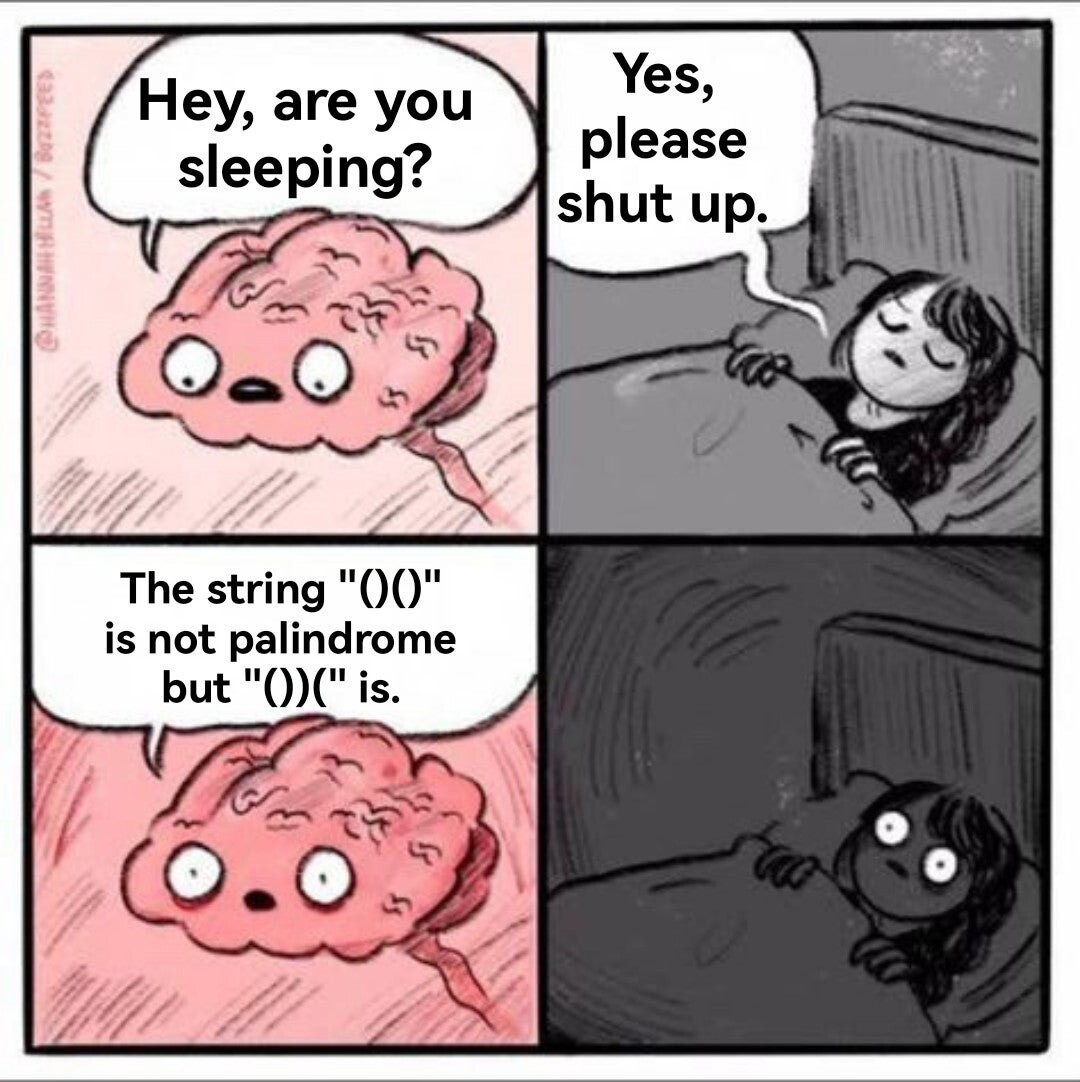
c.reider 
c_reider@sonomu.club
oh no this version of the Hannah Hillam Are you going to sleep? meme is… just, oh no
Jeremi M Gosney 
epixoip@infosec.exchange
I recently wrote a post detailing the recent #LastPass breach from a #password cracker's perspective, and for the most part it was well-received and widely boosted. However, a good number of people questioned why I recommend ditching LastPass and expressed concern with me recommending people jump ship simply because they suffered a breach. Even more are questioning why I recommend #Bitwarden and #1Password, what advantages they hold over LastPass, and why would I dare recommend yet another cloud-based password manager (because obviously the problem is the entire #cloud, not a particular company.)
So, here are my responses to all of these concerns!
Let me start by saying I used to support LastPass. I recommended it for years and defended it publicly in the media. If you search Google for "jeremi gosney" + "lastpass" you'll find hundreds of articles where I've defended and/or pimped LastPass (including in Consumer Reports magazine). I defended it even in the face of vulnerabilities and breaches, because it had superior UX and still seemed like the best option for the masses despite its glaring flaws. And it still has a somewhat special place in my heart, being the password manager that actually turned me on to password managers. It set the bar for what I required from a password manager, and for a while it was unrivaled.
But things change, and in recent years I found myself unable to defend LastPass. I can't recall if there was a particular straw that broke the camel's back, but I do know that I stopped recommending it in 2017 and fully migrated away from it in 2019. Below is an unordered list of the reasons why I lost all faith in LastPass:
- LastPass's claim of "zero knowledge" is a bald-faced lie. They have about as much knowledge as a password manager can possibly get away with. Every time you login to a site, an event is generated and sent to LastPass for the sole purpose of tracking what sites you are logging into. You can disable telemetry, except disabling it doesn't do anything - it still phones home to LastPass every time you authenticate somewhere. Moreover, nearly everything in your LastPass vault is unencrypted. I think most people envision their vault as a sort of encrypted database where the entire file is protected, but no -- with LastPass, your vault is a plaintext file and only a few select fields are encrypted. The only thing that would be worse is if...
- LastPass uses shit #encryption (or "encraption", as @sc00bz calls it). Padding oracle vulnerabilities, use of ECB mode (leaks information about password length and which passwords in the vault are similar/the same. recently switched to unauthenticated CBC, which isn't much better, plus old entries will still be encrypted with ECB mode), vault key uses AES256 but key is derived from only 128 bits of entropy, encryption key leaked through webui, silent KDF downgrade, KDF hash leaked in log files, they even roll their own version of AES - they essentially commit every "crypto 101" sin. All of these are trivial to identify (and fix!) by anyone with even basic familiarity with cryptography, and it's frankly appalling that an alleged security company whose product hinges on cryptography would have such glaring errors. The only thing that would be worse is if...
- LastPass has terrible secrets management. Your vault encryption key always resident in memory and never wiped, and not only that, but the entire vault is decrypted once and stored entirely in memory. If that wasn't enough, the vault recovery key and dOTP are stored on each device in plain text and can be read without root/admin access, rendering the master password rather useless. The only thing that would be worse is if...
- LastPass's browser extensions are garbage. Just pure, unadulterated garbage. Tavis Ormandy went on a hunting spree a few years back and found just about every possible bug -- including credential theft and RCE -- present in LastPass's browser extensions. They also render your browser's sandbox mostly ineffective. Again, for an alleged security company, the sheer amount of high and critical severity bugs was beyond unconscionable. All easy to identify, all easy to fix. Their presence can only be explained by apathy and negligence. The only thing that would be worse is if...
- LastPass's API is also garbage. Server-can-attack-client vulns (server can request encryption key from the client, server can instruct client to inject any javascript it wants on every web page, including code to steal plaintext credentials), JWT issues, HTTP verb confusion, account recovery links can be easily forged, the list goes on. Most of these are possibly low-risk, except in the event that LastPass loses control of its servers. The only thing that would be worse is if...
- LastPass has suffered 7 major #security breaches (malicious actors active on the internal network) in the last 10 years. I don't know what the threshold of "number of major breaches users should tolerate before they lose all faith in the service" is, but surely it's less than 7. So all those "this is only an issue if LastPass loses control of its servers" vulns are actually pretty damn plausible. The only thing that would be worse is if...
- LastPass has a history of ignoring security researchers and vuln reports, and does not participate in the infosec community nor the password cracking community. Vuln reports go unacknowledged and unresolved for months, if not years, if not ever. For a while, they even had an incorrect contact listed for their security team. Bugcrowd fields vulns for them now, and most if not all vuln reports are handled directly by Bugcrowd and not by LastPass. If you try to report a vulnerability to LastPass support, they will pretend they do not understand and will not escalate your ticket to the security team. Now, Tavis Ormandy has praised LastPass for their rapid response to vuln reports, but I have a feeling this is simply because it's Tavis / Project Zero reporting them as this is not the experience that most researchers have had.
You see, I'm not simply recommending that users bail on LastPass because of this latest breach. I'm recommending you run as far way as possible from LastPass due to its long history of incompetence, apathy, and negligence. It's abundantly clear that they do not care about their own security, and much less about your security.
So, why do I recommend Bitwarden and 1Password? It's quite simple:
- I personally know the people who architect 1Password and I can attest that not only are they extremely competent and very talented, but they also actively engage with the password cracking community and have a deep, *deep* desire to do everything in the most correct manner possible. Do they still get some things wrong? Sure. But they strive for continuous improvement and sincerely care about security. Also, their secret key feature ensures that if anyone does obtain a copy of your vault, they simply cannot access it with the master password alone, making it uncrackable.
- Bitwarden is 100% open source. I have not done a thorough code review, but I have taken a fairly long glance at the code and I am mostly pleased with what I've seen. I'm less thrilled about it being written in a garbage collected language and there are some tradeoffs that are made there, but overall Bitwarden is a solid product. I also prefer Bitwarden's UX. I've also considered crowdfunding a formal audit of Bitwarden, much in the way the Open Crypto Audit Project raised the funds to properly audit TrueCrypt. The community would greatly benefit from this.
Is the cloud the problem? No. The vast majority of issues LastPass has had have nothing to do with the fact that it is a cloud-based solution. Further, consider the fact that the threat model for a cloud-based password management solution should *start* with the vault being compromised. In fact, if password management is done correctly, I should be able to host my vault anywhere, even openly downloadable (open S3 bucket, unauthenticated HTTPS, etc.) without concern. I wouldn't do that, of course, but the point is the vault should be just that -- a vault, not a lockbox.
I hope this clarifies things! As always, if you found this useful, please boost for reach and give me a follow for more password insights!
𒀭𒂗𒆠 ENKI ][e
enkiv2@eldritch.cafepeople keep saying the fediverse doesn't have QTs but i've seen some of y'all and you are very cute
Alpha Chen
alphaAlways enjoy The Pudding’s interactive articles, and this one about inequities in wealth due to luck even moreso. https://pudding.cool/2022/12/yard-sale/
Yukihiro Matz Matsumoto
matz@ruby.socialMerry Christmas & Happy Holidays!
.. and Ruby3.2 is released: https://www.ruby-lang.org/en/news/2022/12/25/ruby-3-2-0-released/
Jeremi M Gosney 
epixoip@infosec.exchange
Many of you have been asking for my thoughts on the #LastPass breach, and I apologize that I'm a couple days late delivering.
Apart from all of the other commentary out there, here's what you need to know from a #password cracker's perspective!
Your vault is encrypted with #AES256 using a key that is derived from your master password, which is hashed using a minimum of 100,100 rounds of PBKDF2-HMAC-SHA256 (can be configured to use more rounds, but most people don't). #PBKDF2 is the minimum acceptable standard in key derivation functions (KDFs); it is compute-hard only and fits entirely within registers, so it is highly amenable to acceleration. However, it is the only #KDF that is FIPS/NIST approved, so it's the best (or only) KDF available to many applications. So while there are LOTS of things wrong with LastPass, key derivation isn't necessarily one of them.
Using #Hashcat with the top-of-the-line RTX 4090, you can crack PBKDF2-HMAC-SHA256 with 100,100 rounds at about 88 KH/s. At this speed an attacker could test ~7.6 billion passwords per day, which may sound like a lot, but it really isn't. By comparison, the same GPU can test Windows NT hashes at a rate of 288.5 GH/s, or ~25 quadrillion passwords per day. So while LastPass's hashing is nearly two orders of magnitude faster than the < 10 KH/s that I recommend, it's still more than 3 million times slower than cracking Windows/Active Directory passwords. In practice, it would take you about 3.25 hours to run through rockyou.txt + best64.rule, and a little under two months to exhaust rockyou.txt + rockyou-30000.rule.
Keep in mind these are the speeds for cracking a single vault; for an attacker to achieve this speed, they would have to single out your vault and dedicate their resources to cracking only your vault. If they're trying 1,000 vaults simultaneously, the speed would drop to just 88 H/s. With 1 million vaults, the speed drops to an abysmal 0.088 H/s, or 11.4 seconds to test just one password. Practically speaking, what this means is the attackers will target four groups of users:
1. users for which they have previously-compromised passwords (password reuse, credential stuffing)
2. users with laughably weak master passwords (think top20k)
3. users they can phish
4. high value targets (celebs, .gov, .mil, fortune 100)
If you are not in this list / you don't get phished, then it is highly unlikely your vault will be targeted. And due to the fairly expensive KDF, even passwords of moderate complexity should be safe.
I've seen several people recommend changing your master password as a mitigation for this breach. While changing your master password will help mitigate future breaches should you continue to use LastPass (you shouldn't), it does literally nothing to mitigate this current breach. The attacker has your vault, which was encrypted using a key derived from your master password. That's done, that's in the past. Changing your password will re-encrypt your vault with the new password, but of course it won't re-encrypt the copy of the vault the attacker has with your new password. That would be impossible unless you somehow had access to the attacker's copy of the vault, which if you do, please let me know?
A proper mitigation would be to migrate to #Bitwarden or #1Password, change the passwords for each of your accounts as you migrate over, and also review the MFA status of each of your accounts as well. The perfect way to spend your holiday vacation! Start the new year fresh with proper password hygiene.
For more password insights like this, give me a follow!
Katherine Alejandra Cross
Quinnae_Moon@wandering.shopIt appears, at least in my little archipelago of Mastodons, that there's a Great Quote-Tweet debate happening.
One person I respect asked pointedly to see data that proved QTs were abusive. Since I've been researching affordances of social media platforms I pulled some bits and bobs out of my hideous pile of papers and thought I'd share some insights with y'all about this question.
Cards on the table: I think QTs are a net negative. But nothing's ever simple.